The Current State of IoT Cybersecurity
The Current State of IoT Cybersecurity
- Last Updated: December 2, 2024
Kayla Matthews
- Last Updated: December 2, 2024



October is National Cyber Security Awareness Month (NCSAM), and what better time to talk about the current state of IoT cybersecurity?
IoT devices range from smart speakers to giant machine-to-machine industrial networks. Connected devices are becoming extremely popular across a range of verticals.
Because of both the ability of the devices to connect to the internet and their widespread usage, IoT products are prime targets for hacks.
A Relatively New Kind of Hack
Historical data indicates the first wave of IoT attacks arrived in 2016. In that case, the hackers mainly targeted IoT devices including routers and IP cameras. They then turned those devices into botnets—infected devices controlled as a group. Unbeknownst to their owners, hackers leverage the collective power of a "botnet" to launch malicious attacks at scale.
Unfortunately, cybercriminals have only become bolder and more creative in their methods since the aforementioned 2016 hacks. One recent hack targeted a device that controlled up to 16 CCTV cameras, putting them at risk for remote hijacking. The security vendor that discovered the flaw and warned that it could affect up to 2,500 camera models.
Numerous Specific Threats
One known security risk is that the companies behind IoT devices with known vulnerabilities don't fully patch the devices. Sometimes, they ignore security as a whole due to inexperience or wanting to release the hardware too quickly.
Network-level attacks are among the security risks for IoT devices. A hacker may carry out a distributed denial of service (DDoS) attack, which floods network-connected devices with too many requests. The server cannot process legitimate requests under the load. The hack often shuts down entire websites.
IoT devices may be compromised by RFID spoofing as well. It allows cybercriminals to create fake RFID signals that let them read and record data transmissions.
However, the biggest security challenges for IoT professionals to overcome are software threats. Hackers depend on Trojan viruses, malicious scripts, and malware to disable IoT systems.
Consumers Contribute to the Security Problem
A report from Mozilla mentions there will be up to 30 billion connected devices by 2020. Unfortunately, IoT security isn't just a concern for the professionals who actively try to keep hackers from infiltrating systems. Consumers should proactively reduce security threats as well.
Many people get so excited by the flashy features of a new IoT gadget, such as a security camera that recognizes faces or a fitness wearable that measures sleep patterns, that they overlook basic security protocols. It's important to set strong passwords and regularly update devices to incorporate the newest security patches.
The Mozilla study points out that many device owners' primary concern is that gadgets just work as expected. When they do function as advertised, securing those devices becomes an afterthought. Only after something unsettling happens are they reminded of the potential dangers.
Besides gaining an overview of what constitutes IoT security and why the topic matters, it's essential for individuals to know the current state of cybersecurity in the IoT sector and what's on the horizon.
Hacks Are Costly
Statistics about hacks in general—not just those related to IoT systems—show the annual cost to the U.S. economy is $100 billion. They result in the loss of approximately 100,000 jobs. Hacks exist that weren't conceivable in past eras. For example, "voice hacking" (or emulation) is a new kind of identity theft. That's concerning for many reasons. For example, since so many people use their voices to activate the personal assistants in IoT devices (e.g. Alexa and Google Assistant), a voice hack on an IoT network could affect much more than your daily calendar or reminders. People must also consider that some IoT devices contain particularly sensitive data, such as a person's medical data.
Malware is Especially on the Rise
Data from Kaspersky Lab suggests people should be especially on alert for malware attacks related to their IoT devices. When the research team compared 2017 statistics to the information collected in the first half of this year, they found a threefold increase in the malware samples attacking smart gadgets.
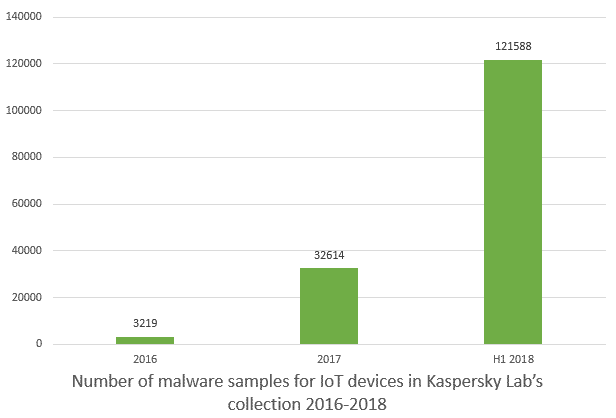
Image Credit: Kaspersky Lab
It's also worth noting that malware made for IP cameras is still of interest to hackers, just as it was in 2016. In one instance, the researchers associated with Kaspersky Labs found that a type of malware for those devices infected 57,000 units in only a week.
[embed]https://youtu.be/5fVBB84OiAo?t=164[/embed]
Trojans at the Gateway
Content in the Kaspersky Lab report mentioned a new Trojan virus with an apparently broad reach. Referred to as the VPNFilter Trojan, it disables IoT devices and makes them virtually self-destruct. VPNFilter overwrites critical parts of the device's firmware with useless data and then reboots the machine.
Researchers aren't sure how the virus gets distributed. The first report published about it discussed approximately 500,000 infected devices, including those from major names like Huawei, Netgear, and ASUS.
Cultivating a More Secure Ecosystem for IoT Systems
Given the severity of the issues mentioned above, it's especially eye-opening that only 10 percent of device manufacturers felt fully confident their devices had adequate security precautions in place. That could change due to a new security initiative from AT&T and Ericsson, but the culture of lax security in IoT hardware vendors is likely to be slow to change.
The brands want to facilitate device makers receiving security certifications. Eventually, such designations could be a selling point for consumers who are worried about IoT security and want to safeguard themselves against possible issues.
The project, known as the Cybersecurity Certification Program, will collect data about known IoT vulnerabilities and provide it to manufacturers. Brands will be able to accommodate for those threats as promptly as possible, and developers can stay aware of the biggest IoT risks.
California Passes the First IoT Security Bill
California recently became the first state to approve an IoT security bill that will come into effect in 2020. The law sets minimum security standards for IoT devices, including mandating that preset passwords be unique to each device. Could the bill be a precedent for further regulation in other states and countries or will the buzz fizzle out? Must we wait for a big hack before facing down the current state of IoT cybersecurity?
Plans to Reinforce IoT Security
There's no doubt IoT devices have worrisome security-related weak spots. However, there is a gradually increasing awareness from the IoT industry—and the broader public—about the need to face these problems together.
The Most Comprehensive IoT Newsletter for Enterprises
Showcasing the highest-quality content, resources, news, and insights from the world of the Internet of Things. Subscribe to remain informed and up-to-date.
New Podcast Episode

Can AI Design IoT Hardware?
Related Articles