Balancing Optimism for a Hong Kong Smart City Blueprint
Balancing Optimism for a Hong Kong Smart City Blueprint
- Last Updated: December 2, 2024
Guest Writer
- Last Updated: December 2, 2024



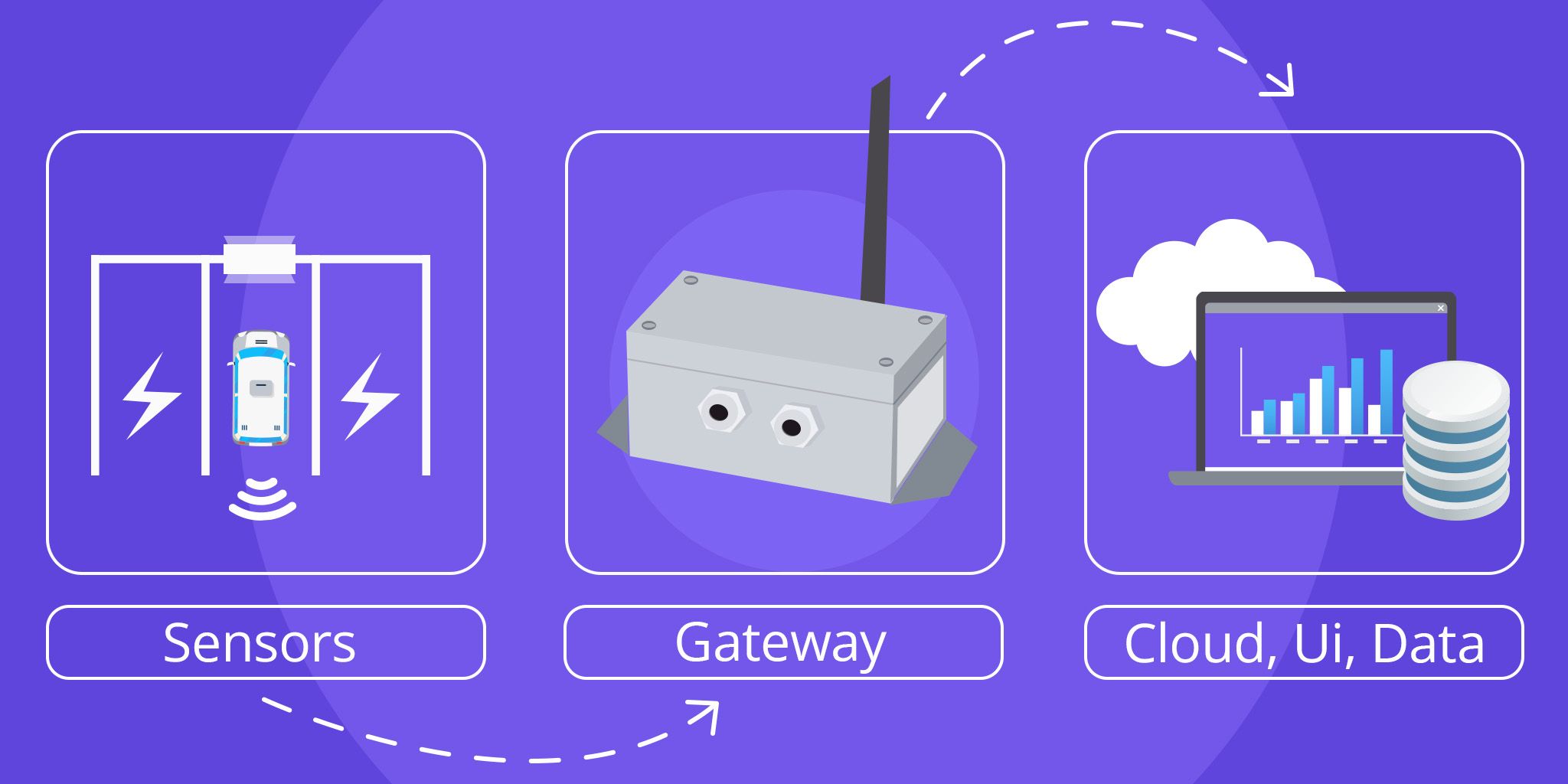
In Hong Kong, the HKSAR Government (the “Government”) announced plans to conduct pilot studies of developing a Smart City with the Internet of Things (IoT) and fifth-generation (5G) mobile networks as early as 2015. The idea behind the Government’s Smart City Blueprint is that 5G mobile networks would play a pivotal role for its smart city development by facilitating ultra-high-speed, ultra-reliable and low latency communications, and by provisioning network capacities for largescale device-to-device communication that would ultimately enable scalable implementation of IoT devices and services across the city.
Whilst the Government has stated that their Smart City Blueprint is people-centric with its core missions heavily focused on higher quality of living, prosperity of business and eco-friendliness, it failed to address growing concerns with cybersecurity and personal data protection that associate with the adoption of IoT.
Cybersecurity concerns are a major obstacle to smart city success. Is there potential of having a licensing regime for IoT developers in Hong Kong?
Concerns with IoT
It is often said that the technology at this stage is vulnerable to hacking as they open channels for unwanted surveillance. Such arguments should not be hastily dismissed as they have recently found solid ground with these concerns having been echoed and acknowledged by the US Department of Homeland Security (DHS) which viewed IoT as a major matter of national security.
Considering IoT as the cornerstone of the Government’s ‘Smart City Blueprint’ and it has been five years since the project was conceived, with Hong Kong paving its way for mass implementation of IoT applications, there appears to be an oversight or a lack of consideration given to the potential cybersecurity and data risk impacts of widespread IoT usage at its current form.
One major obstacle to reaching cybersecurity and data protection utopia is that these devices were never developed with the safety or security of data at the core of their designs. Current industry practices dictate that IoT devices are to be designed to have the bare minimum computational power that is needed for their tasks and therefore by their nature, typically lack the needed computational power to run cybersecurity software. However, with consumers growing and improving their understanding of cybersecurity and personal data risks that come with the adoption and usage of IoT, there will come a time when current industry practices and IoT standards no longer satisfy the demands of the market.
Security Through Legislation and Licensing
To increase the incentive to change industry practices and improve the practicality of built-in cybersecurity capabilities in IoT products, major changes are required to regulate the industry when it comes to design, manufacturing and consumption.
Earlier this year, the UK Government unveiled a possible new regulatory regime aimed at mitigating security risks associated with IoT by changing the way these products are produced, retailed and supported throughout their lifetime. If successfully legislated, IoT manufacturers will have to abide by the following requirements:
- IoT devices must each have their own unique passwords that cannot be reset to universal factory setting;
- IoT manufacturers must set up a public point of contact for consumers to report flaws of their purchased products; and
- IoT manufacturers must explicitly state the minimum length of time that a device will continue to receive security updates at the point of sale.
Separate to the above, optional legislation under the proposed regulatory plan invokes a mandatory labeling system that requires IoT manufacturers to self-assess and implement a security label on their consumer IoT products.
The developments in UK are surely exciting, yet, should Hong Kong enact a similar regulatory regime as to acclimatize to the newest IoT landscape?
Current IoT Legislation in Hong Kong
At the moment, there is no specific legislation on IoT in Hong Kong. Most of the issues relating to IoT are dealt with by existing legislations.
For example, in relation to data protection, the Personal Data (Privacy) Ordinance (Cap. 486) (“PDPO”) applies to IoT developers who collect personal data from its users. Under the current Data Protection Principle (4) (“DPP4”), all practicable steps shall be taken to ensure that personal data held by a data user are protected against unauthorized or accidental access, processing, erasure, loss or use having particular regard to, amongst other things, any security measures incorporated into any equipment in which the data is stored.
In addition, if the IoT developer engages a data processor (whether within or outside Hong Kong) to process the data on the data user’s behalf, the IoT developer (as a data user) must adopt contractual or other means to prevent unauthorized or accidental access, processing, erasure, loss or use of the data transferred to the data processor for processing (DPP4 (2) of PDPO).
It is important to note that contraventions of the DPPs do not constitute an offense itself, but the Privacy Commissioner for Personal Data (PCPD) may serve an enforcement notice on the IoT developer (as a data user) requesting it to rectify or remedy any data related issues. If the IoT developer contravenes an enforcement notice, the IoT developer will commit an offense and is liable for HK$50,000 and to imprisonment for 2 years, or for second or subsequent conviction, a fine at HK$100,000 and to imprisonment for 2 years (s.50A(1) of the PDPO).
Code of Practice on the Operation and Management of IoT Devices
Although there is no specific IoT legislation in Hong Kong, the Communications Authority (CA) in Hong Kong announced on 1st December 2017 to create a new licensing regime for the provision of WIoT platforms and service providers providing wireless connections for their customers to connect IoT devices to the public telecommunications networks using the shared frequency band of 920-925 MHz with a view to underpinning the preparation of Hong Kong for embracing the new era of IoT and the 5G mobile services, as well as various smart city applications. To date, there are 3 WIoT licenses issued.
Furthermore, the CA has also issued a Code of Practice on the Operation and Management of IoT Devices (“CoP”) to provide practical guidance to WIoT licensees in regards to the provision of satisfactory service and the protection and promotion of the interests of consumers of telecommunications goods and services.
The CoP is developed for the operation and management of IoT devices connected to public telecommunications networks to:
- ensure the provision of satisfactory service by IoT service providers;
- strengthen consumer protection;
- enhance user confidence in using IoT devices connecting to public telecommunication networks; and
- serve as a reference for non-telecommunications licensees (such as device manufacturers, vendors, application developers) in formulating requirements and practices regarding the operation and management of IoT devices/services.
It is important to note that the CoP is merely a ‘best practice’ guide for IoT service providers to observe on a voluntary basis. For non-telecommunications licensees such as device manufacturers, vendors, and application developers who may supply and deploy IoT devices in the telecommunications and other business sectors (e.g. personal, leisure, household, transport, medical or financial sectors), the CoP only serves as a reference to assist in formulating suitable requirements and practices regarding the operation and management of IoT devices/services (para. 3 of the CoP).
Out of the CoP’s ten recommended best practices, the following are worth highlighting (para. 5 of the CoP):
- recommendation for unique usernames and strong passwords to be adopted for IoT devices;
- users should be provided with a point of contact to report security issues;
- software of the IoT devices should be updated in a timely manner and should not impact on the functions of the devices;
- sensitive data should be stored securely in the IoT devices to prevent unauthorized access and modification; and
- personal data should be protected in accordance with the PDPO.
The CoP also recommends that IoT service providers should regularly conduct assessments on potential risks relevant to their daily operation and management of IoT devices (para. 6 of the CoP).
The recommendations are mostly aligned with the UK’s proposed regulatory regime, and the CA has also taken reference from the UK’s Code of Practice for Consumer IoT Security when designing the CoP[10]. However, we should stress that since the CoP is merely a ‘best practice’ reference for IoT device manufacturers, the CoP has no legal binding.
Moreover, the CA’s WIoT licensing regime only applies to wireless IoT service providers and does not apply to IoT device manufacturers, this may be too narrow in terms of scope and likely to be inadequate in addressing the specific issues concerning IoT as highlighted above.
Government’s Review of Telecommunications Regulatory Framework
Apart from the CA’s WIoT licensing regime and the CoP, the Government’s Commerce and Economic Development Bureau (“CEDB”) has completed a public consultation on the Review of Telecommunications Regulatory Network (RTRN) in February 2019.
The RTRN aims to review the telecommunications regulatory framework under the Telecommunications Ordinance (Cap. 106) (“TO”) to ensure that it is in line with the advancement of telecommunications technologies such as 5G and IoT.
The CEDB has put forward four recommendations, namely:
- to regulate telecommunications functions of devices in the 5G and IoT era through TO and CA;
- to protect underground telecommunications infrastructure by introducing criminal liabilities for negligent damage;
- to streamline mechanism for issuing non-carrier licenses; and
- to expand the scope of the CA’s decisions made under the TO that could be dealt with by the proposed appeal mechanism.
Although the RTRN provides better regulatory direction in developing the technological infrastructure in Hong Kong, it is nonetheless disappointed to note that the RTRN has not adequately dealt with the specific issues concerning security and data privacy issues in relation to IoT devices.
Concluding Remarks
Could the answer for a future of safe IoT-enabled Smart City be safeguarded through a comprehensive licensing regime? Or could it be done through a more product-centric liability proof scheme? These are some of the ‘tip of the iceberg’ issues that stakeholders in Hong Kong should start thinking about.
Lawmakers in Hong Kong should also start thinking about how the specific issues in relation to IoT’s security and data protection can be addressed. For example, through a highly enforceable robust framework or a government-backed licensing regime.
Should Hong Kong enact similar legislation to the UK regulatory regime? It may be possible for lawmakers to introduce a similar regulation that acclimatizes to the current tech landscape in Hong Kong. Yet, as many IoT hardware manufacturers are located in PRC with Hong Kong merely contributing as an IoT retail and service hub, it is difficult to assess whether such a regulatory regime would be effective.
The Most Comprehensive IoT Newsletter for Enterprises
Showcasing the highest-quality content, resources, news, and insights from the world of the Internet of Things. Subscribe to remain informed and up-to-date.
New Podcast Episode

Can AI Design IoT Hardware?
Related Articles
The $240 Billion Shield: Navigating the Global Cybersecurity Surge of 2026
January 22, 2026

Securing the Mobile IoT Workforce: Why Enterprise Mobile Security Is Critical Infrastructure
January 14, 2026

Why AI Risk Visibility Is the Future of Enterprise Cybersecurity Strategy: Q&A With Srikanth Ambatipudi
January 2, 2026